With the amount of information stored and shared online, social media security is more important than ever.
There’s no doubt social has made the world a more connected place. In most cases, that’s a good thing. But all those connections also create unprecedented access to people’s and business’ information. And that can be a very bad thing when hackers and scammers get involved.
Giving up social media is not a reasonable option. But neither is it reasonable to carry on as if social networks are always safe and secure. You need to take steps to protect your company against some of the most common social media security threats. Here’s where to start.
Bonus: Get the step-by-step social media strategy guide with pro tips on how to grow your social media presence.
Common social media security risks
Unattended social media accounts
It can be a good idea to reserve your brand’s handle on all social media channels, even if you don’t plan to use them all right away. This allows you to maintain a consistent presence across networks, making it easy for people to find you.
But it’s important not to ignore the accounts you don’t use yet, those that you’ve stopped using, or those you don’t use often.
Idle social accounts can be the target of hackers, who could start posting fraudulent messages under your name.
Knowing the account is unmonitored, once they gain control, they could send anything from false information that’s damaging to your business to virus-infected links that cause serious problems for followers. And you won’t even notice until your customers start coming to you for help.
Human error
Everyone makes mistakes. In today’s busy world, it is all too easy for an employee to accidentally expose the company to threats online. In fact, 77 percent of respondents to the 20th EY Global Information Security Survey said that a careless member of staff was the most likely source of a cybersecurity threat.
Something as simple as clicking on the wrong link or downloading the wrong file could wreak havoc.
Bonus: Register for our upcoming webinar, “Build and Protect Your Brand on Social Media,” to learn everything you need to know about online reputation management—from potential risks to mitigation tactics (and tools).
Third-party apps
Even if you have your own social accounts on lockdown, hackers may be able to gain access through vulnerabilities in third-party apps that integrate with the big social networks.
For example, hackers gained access to the Twitter accounts of Forbes and Amnesty International using a flaw in the Twitter Counter app, used for Twitter analysis.
Phishing attacks and scams
Phishing scams use social media to trick people into handing over personal information (like banking details, passwords, or business information).
A recent social media scam involved false reports that the actor Rowan Atkinson had died. (The Mr. Bean and Blackadder actor is still very much alive.)
What looked like a video link actually directed users to a page that said their computer had been locked, with a phone number to call for support. Rather than a support team, the phone line connected to scammers looking for credit card numbers and personal information. Worse, the “support software” offered was actually a virus.
Filmmaker Tyler Perry recently posted a video to his Facebook account warning fans not to fall victim to giveaway scams using his name. He said his team has to shut down, “10, 20, 30 of these things” every day.
Posted by Tyler Perry on Tuesday, July 10, 2018
Imposter accounts
The number of fraudulent social support accounts doubled between the third quarter of 2016 and Q3 2017. Those accounts can target your customers, tricking them into handing over confidential information and tarnishing your reputation in the process.
Imposter accounts may also try to con your employees into handing over login credentials for corporate systems.
Malware attacks and hacks
Social media hackers are becoming more sophisticated. Hackers have gained access to big-name Twitter accounts, from Kylie Jenner and Mark Zuckerberg, to several HBO shows.
//twitter.com/bronze_bombSHEL/status/898176195409436673?ref_src=twsrc%5Etfw
Those hacks were fairly benign. Others are much more serious.
For example, hackers used a fake profile to connect with employees of targeted organizations, sharing a file that gave the attackers remote access to the victims’ work computers.
Privacy settings
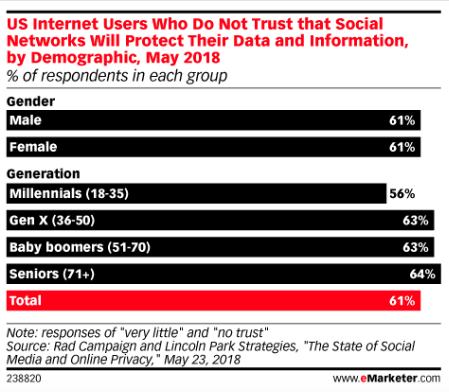
People seem to be well aware of the potential privacy risks of using social media. A recent survey found that nearly two-thirds of people have “very little” or “no” trust in social networks when it comes to privacy protection.
But those concerns don’t stop us from using our favorite social channels.
For brands, the risk to privacy is higher because of the number of people who use social media in the office—for business and personal use.
Unsecured mobile phones
Mobile devices are the most popular way to access social networks. Using each network’s mobile app makes it easy to access social media accounts with just one tap.
That’s great as long as your phone stays in your possession. But if your phone, or an employee’s phone, is lost or stolen, one-tap access makes it easy for a thief to access social accounts. And then they can message all of your connections with phishing or malware attacks.
Protecting the device with a password helps, but more than half of mobile phone users leave their phones unlocked.
8 social media security tips and best practices
1. Create a social media policy
If your business is using social media—or getting ready to—you need a social media policy.
These guidelines outline how your business and its employees should use social media responsibly. This will not only protect your from security threats, but bad PR or legal trouble as well.
At minimum, your social media policy should include:
- Brand guidelines that explain how to talk about your company on social
- Rules related to confidentiality and personal social media use
- Which departments or team members are responsible for each social media account
- Guidelines related to copyright and confidentiality
- Guidelines on how to create an effective password and how often to change passwords
- Expectations for keeping software and devices updated
- How to identify and avoid scams, attacks, and other security threats
- Who to notify and how to respond if a social media security concern arises
For more details, check out our step-by-step guide to creating a social media policy, including loads of examples from different industries.
Bonus: Get the step-by-step social media strategy guide with pro tips on how to grow your social media presence.
2. Train your staff on social media security best practices
Even the best social media policy won’t protect your organization if your employees don’t follow it. While your policy should be easy to understand, training will give employees the chance to engage, ask questions, and get a sense of how important it is to follow.
These training sessions are also an opportunity to review the latest threats on social, and talk about whether there are any sections of the policy that need updating.
And it’s not all doom and gloom. Social media training also equips your team to use the tools effectively. When employees understand best practices, they’ll feel confident using social for both personal and professional purposes.
3. Limit social media access
While you may be focused on threats coming from outside your organization, PriceWaterhouseCoopers found employees are more likely to cause cyber security incidents than are hackers. Limiting access to your social accounts is the best way to keep them secure.
You may have whole teams of people working on social media messaging, post creation, or customer service. But that doesn’t mean everyone needs the ability to post. And it doesn’t mean that everyone needs to know the passwords to your social accounts.
The first line of defense is to limit the number of people who can post on your accounts. Think carefully about who needs posting ability and why.
Once you’ve decided who can post, use software like Hootsuite to give the right people the right account access. This way, they never need to know the individual login information for any social network account. If the person leaves your company, you can disable their account without having to change all the social networks passwords.
4. Set up a system of approvals for social posts
Z-Burger recently faced a major crisis after a marketing contractor used a photo of a slain journalist in an extremely inappropriate Twitter post. No one at Z-Burger saw the tweet before it was posted, since they had given the contractor the ability to publish directly to their account.
The owner of Z-Burger was horrified when he saw the tweet and took action to delete the offensive post right away. But if he had set up an approval system, he or his staff would have reviewed the tweet before it was published. And the crisis would have been averted.
You can use Hootsuite to give employees or contractors the ability to draft messages, preparing them so they’re all set to post at the press of a button. But leave that last button press to a trusted person on your team.
//www.youtube.com/watch?v=wvp9VZcJRO0
5. Put someone in charge
Designating a key person as the eyes and ears of your social presence can go a long way towards mitigating risks. This person should own your social media policy, monitor your brand’s social presence, and determine who has publishing access. This person should also be a key player in the development of your social media marketing strategy.
This person will likely be a senior person on your marketing team. But they should maintain a good relationship with your company’s IT department to ensure marketing and IT work together to mitigate risk.
This person is also who team members should turn to if they ever make a mistake on social that might expose the company to risk of any kind—from security to a damaged reputation. This way the company can initiate the appropriate response.
6. Monitor your accounts and engage in social listening
As mentioned at the start, unattended social accounts are ripe for hacking. Keep an eye on all of your social channels—from the ones you use every day to the ones you’ve registered but never used at all. Assign someone to check that all of the posts on your accounts are legitimate. Cross-referencing your posts against your content calendar is a great place to start.
Follow up on anything unexpected. Even if a post seems legitimate, it’s worth digging into if it strays from your content plan. It may be simple human error. Or, it may be a sign that someone has gained access to your accounts and is testing the water before posting something more malicious.
You also need to watch for imposter accounts, inappropriate mentions of your brand by employees (or anyone else associated with the company), and negative conversations about your brand.
You can learn how to monitor all the conversations and accounts relevant to your brand in our complete guide to social media listening.
7. Invest in security technology
No matter how close an eye you keep on your social channels, you can’t monitor them 24 hours a days—but software can. Solutions like ZeroFOX will automatically alert you of security risks.
When you integrate ZeroFOX with your Hootsuite dashboard, it will alert you to dangerous, threatening, or offensive content targeting your brand; malicious links posted on your social accounts; scams targeting your business and customers; and fraudulent accounts impersonating your brand. It also helps protect against hacking and phishing attacks.
//www.youtube.com/watch?v=T3duCIyqm1g
8. Perform a regular audit
Social media security threats are constantly changing. Hackers are always coming up with new strategies, and new scams and viruses can emerge at any time. Scheduling regular audits of your social media security measures will help keep you ahead of the bad actors.
At least once a quarter, be sure to review:
- Social network privacy settings. Social media companies routinely update their privacy settings, which can have an impact on your account. For example, a social network might update its privacy settings to give you more precise control over how your data is used.
- Access and publishing privileges. Perform a scan of who has access to and publishing rights on your social media management platform and social accounts and update as needed. Make sure all former employees have had their access revoked, and check for anyone who’s changed roles and no longer needs the same level of access.
- Recent social media security threats. Maintain a good relationship with your company’s IT team so they can keep you informed of any new social media security risks they become aware of. And keep an eye on the news—big hacks and major new threats will be reported in mainstream news outlets.
- Your social media policy. This policy should evolve over time as new networks gain popularity, security best practices change, and new threats emerge. A quarterly review will make sure this document remains useful and helps to keep your social accounts safe.
Use Hootsuite to manage all your social media accounts safely and securely in one place. Mitigate risks and stay compliant with our best-in-class security features, apps, and integrations.
//blog.hootsuite.com/social-media-security-for-business/
On – 08 Aug, 2018 By Christina Newberry